A crippling flaw in a widely used code library has fatally undermined the security of millions of encryption keys used in some of the highest-stakes settings, including national identity cards, software- and application-signing, and trusted platform modules protecting government and corporate computers.
- Encryption Rsa 2048 Key Generated For This Computer Game
- Encryption Rsa 2048 Key Generated For This Computer Windows 7
- 2048 Bit Rsa Key
- Rsa 2048 Bit Encryption
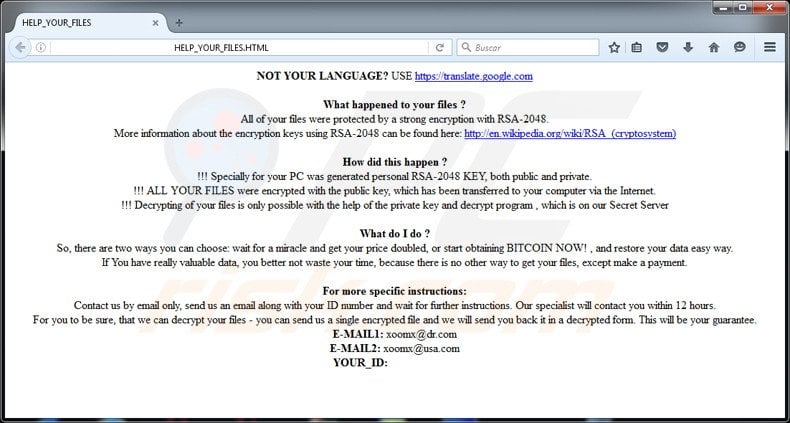
Dec 10, 2018 RSA encryption can be used in a number of different systems. It can be implemented in OpenSSL, wolfCrypt, cryptlib and a number of other cryptographic libraries. As one of the first widely used public-key encryption schemes, RSA laid the foundations for much of our secure communications. Dec 06, 2015 RSA-2048/cryptoware is a high risk randomware that has affected tens of thousands of computer users. It will encrypt the personal documents found on victim’s computer using RSA-2048 key (AES CBC 256-bit encryption algorithm) after infiltration. You can read this article and learn how to remove this kind of ransom ware.
The weakness allows attackers to calculate the private portion of any vulnerable key using nothing more than the corresponding public portion. Hackers can then use the private key to impersonate key owners, decrypt sensitive data, sneak malicious code into digitally signed software, and bypass protections that prevent accessing or tampering with stolen PCs. The five-year-old flaw is also troubling because it's located in code that complies with two internationally recognized security certification standards that are binding on many governments, contractors, and companies around the world. The code library was developed by German chipmaker Infineon and has been generating weak keys since 2012 at the latest.
The flaw is the one Estonia's government obliquely referred to last month when it warned that 750,000 digital IDs issued since 2014 were vulnerable to attack. Estonian officials said they were closing the ID card public key database to prevent abuse. On Monday, officials posted this update. Last week, Microsoft, Google, and Infineon all warned how the weakness can impair the protections built into TPM products that ironically enough are designed to give an additional measure of security to high-targeted individuals and organizations.
The RSA-2048 encryption key typical for Cryptowall 3.0 has been reported to strike users’ computers and display a ransomware message. Thus, the threat is also dubbed Ransomware RSA-2048 or may be referred as RSA-2048 virus. Create a 2048-bit RSA private key. Don’t share this key with anyone, use it only in the EDD FastSpring plugin settings. This key will be used to encrypt the orders. Use this command to generate the privatekey.pem file which will contain your private key. I am trying to encrypt and decrypt the data with RSA 2048. We have one public key and private key and will be using same throughout. But the problem is, when I decrypt, I am getting javax.crypto. When a key is generated with openssl genrsa, the encryption is selected with a command line argument such as -aes128. After the key is generated, we can see what encryption was used in the file.
Completely broken
'In public key cryptography, a fundamental property is that public keys really are public—you can give them to anyone without any impact in security,' said Graham Steel, CEO of Cryptosense, which makes software for testing encryption security. 'In this work, that property is completely broken.' He continued:
It means that if you have a document digitally signed with someone's private key, you can't prove it was really them who signed it. Or if you sent sensitive data encrypted under someone's public key, you can't be sure that only they can read it. You could now go to court and deny that it was you that signed something—there would be no way to prove it, because theoretically, anyone could have worked out your private key.
Both Steel and Petr Svenda, one of the researchers who discovered the faulty library, also warned the flaw has, or at least had, the potential to create problems for elections in countries where vulnerable cards are used. While actual voter fraud would be difficult to carry out, particularly on a scale needed to sway elections, 'just the possibility (although impractical) is troubling as it is support for various fake news or conspiracy theories,' Svenda, who is a professor at Masaryk University in the Czech Republic, told Ars. Invoking the prolific leakers of classified National Security Agency material, Steel added: 'Imagine a Shadowbrokers-like organization posts just a couple of private keys on the Internet and claims to have used the technique to break many more.'
The flaw is the subject of a research paper titled The Return of Coppersmith's Attack: Practical Factorization of Widely Used RSA Moduli, which will be presented on November 2 at the ACM Conference on Computer and Communications Security. The vulnerability was discovered by Slovak and Czech researchers from Masaryk University in the Czech Republic, Enigma Bridge in Cambridge, UK, and Ca' Foscari University in Italy. To give people time to change keys, the paper describing the factorization method isn't being published until it's presented at the conference.
The flaw resides in the Infineon-developed RSA Library version v1.02.013, specifically within an algorithm it implements for RSA primes generation. The library allows people to generate keys with smartcards rather than with general-purpose computers, which are easier to infect with malware and hence aren't suitable for high-security uses. The library runs on hardware Infineon sells to a wide range of manufacturers using Infineon smartcard chips and TPMs. The manufacturers, in turn, sell the wares to other device makers or end users. The flaw affects only keys generated with the RSA algorithm, and then only when they were generated on a smartcard or other embedded device that uses the Infineon library.
To boost performance, the Infineon library constructs the keys' underlying prime numbers in a way that makes the keys prone to a process known as factorization, which exposes the secret numbers underpinning their security. When generated properly, an RSA key with 2048 bits should require several quadrillion years—or hundreds of thousands of times the age of the universe—to be factorized with a general-purpose computer. Factorizing a 2048-bit RSA key generated with the faulty Infineon library, by contrast, takes a maximum of 100 years, and on average only half that. Keys with 1024 bits take a maximum of only three months.
The factorization can be dramatically accelerated by spreading the load onto multiple computers. While costs and times vary for each vulnerable key, the worst case for a 2048-bit one would require no more than 17 days and $40,300 using a 1,000-instance machine on Amazon Web Service and $76 and 45 minutes to factorize an affected 1024-bit key. On average, it would require half the cost and time to factorize the affected keys. All that's required is passing the public key through an extension of what's known as Coppersmith's Attack.
While all keys generated with the library are much weaker than they should be, it's not currently practical to factorize all of them. For example, 3072-bit and 4096-bit keys aren't practically factorable. But oddly enough, the theoretically stronger, longer 4096-bit key is much weaker than the 3072-bit key and may fall within the reach of a practical (although costly) factorization if the researchers' method improves.
To spare time and cost, attackers can first test a public key to see if it's vulnerable to the attack. The test is inexpensive, requires less than 1 millisecond, and its creators believe it produces practically zero false positives and zero false negatives. The fingerprinting allows attackers to expend effort only on keys that are practically factorizable. The researchers have already used the method successfully to identify weak keys, and they have provided a tool here to test if a given key was generated using the faulty library. A blog post with more details is here.
In search of vulnerable keys
The researchers examined keys used in electronic identity cards issued by four countries and quickly found two—Estonia and Slovakia—were issuing documents with fingerprinted keys, both of which were 2048 bits in length, making them practically factorizable. Estonia has disclosed the flaw in what it said were 750,000 of the cards issued since 2014. Ars checked the key used in an e-residency card Ars Senior Business Editor Cyrus Farivar obtained in 2015, and it came back as factorizable.While it has closed its public key database, Estonian government officials have also announced plans to rotate all keys to a format that's not vulnerable, starting in November. The status of Slovakia's system isn't immediately clear. With two of the four countries checked testing positive for fingerprinted keys, a more exhaustive search is likely to identify many more nations issuing cards with factorizable keys.
Next, the researchers examined a sampling of 41 different laptop models that used trusted platform modules. They found vulnerable TPMs from Infineon in 10 of them. The vulnerability is especially acute for TPM version 1.2, because the keys it uses to control Microsoft's BitLocker hard-disk encryption are factorizable. That means anyone who steals or finds an affected computer could bypass the encryption protecting the hard drive and boot sequence. TPM version 2.0 doesn't use factorizable keys for BitLocker, although RSA keys generated for other purposes remain affected. Infineon has issued a firmware update that patches the library vulnerability, and downstream affected TPM manufacturers are in the process of releasing one as well.
The researchers also scanned the Internet for fingerprinted keys and quickly found hits in a variety of surprising places. They found 447 fingerprinted keys—237 of them factorizable—used to sign GitHub submissions, some for very popular software packages. GitHub has since been notified of the fingerprinted keys and is in the process of getting users to change them.
The researchers also found 2,892 PGP keys used for encrypted e-mail, 956 of which were factorizable. The researchers speculated that the majority of the PGP keys were generated using the Yubikey 4, which allows owners to use the faulty library to create on-chip RSA keys. Other functions of the USB device, including U2F authentication, remain unaffected. Yubico has more details here.
The researchers went on to find 15 factorizable keys used for TLS. Strangely, almost all of them contain the string 'SCADA' in the common name field. That raised the possibility the certificates are being used by an organization involved in Supervisory Control And Data Acquisition, which uses computers to control dams, electric substations, and other industrial equipment. All 15 fingerprinted keys have a characteristic involving their prime numbers that is outside the range of what's produced by the faulty Infineon library, raising the possibility there was a modification of it that hasn't yet been documented.
This is the second time in four years that a major crypto flaw has been found hitting a crypto scheme that has passed rigorous certification tests. In 2013, a different set of researchers unearthed flaws in Taiwan's secure digital ID system that would allow attackers to impersonate some citizens. Like the flawed Infineon library, the underlying cryptography in the Taiwanese digital ID was advertised as having passed the FIPS 140-2 Level 2 and the Common Criteria standards. Both certifications are managed by the National Institute of Standards and Technology. Both certifications are often mandatory for certain uses inside government agencies, contractors, and others. In the Taiwanese case, the cards weren't configured properly by the vendor prior to shipping, a condition that meant they weren't tested by NIST.The researchers who uncovered the Infineon library flaw questioned whether the secrecy required by some of the certification process played a role. They wrote:
Our work highlights the dangers of keeping the design secret and the implementation closed-source, even if both are thoroughly analyzed and certified by experts. The lack of public information causes a delay in the discovery of flaws (and hinders the process of checking for them), thereby increasing the number of already deployed and affected devices at the time of detection.
All told, the researchers estimate that Infineon's faulty library may have generated tens of millions of RSA keys in the five or so years it has been commercially available. A good many of them are practically factorizable, but even those that are not are considerably more vulnerable to factorization than federal standards and common-sense security guidelines dictate. RSA keys generated with OpenSSL, PGP-compliant programs, or similar computer programs aren't affected. People who have relied on smartcards or embedded devices for cryptographic functions should test their RSA keys using the researchers' fingerprinting tool. In the event the keys test positive, people should revoke them as soon as possible and generate new ones. Keys using Elliptic Curve Cryptography and other non-RSA methods aren't affected.
It's going to take a while for people to identify all vulnerable keys. They should start by replacing those that are known to be practically factorizable, but eventually all RSA keys generated by the flawed library should go. Cryptographers and engineers within NIST and other standards organizations should also use the failure to learn how to improve their high-security certifications processes.
This post was updated to correct statements about Taiwanese ID cards.
- Cryptography Tutorial
- Cryptography Useful Resources
- Selected Reading
Public Key Cryptography
Unlike symmetric key cryptography, we do not find historical use of public-key cryptography. It is a relatively new concept.
Symmetric cryptography was well suited for organizations such as governments, military, and big financial corporations were involved in the classified communication.
With the spread of more unsecure computer networks in last few decades, a genuine need was felt to use cryptography at larger scale. The symmetric key was found to be non-practical due to challenges it faced for key management. This gave rise to the public key cryptosystems.
The process of encryption and decryption is depicted in the following illustration −
The most important properties of public key encryption scheme are −
STEP – 2We are constantly looking for new associate programmers, so we use this opportunity to invite all those who would like to cooperate with us to contact us by email. Enter product code into origin. Create and control a new generation of, with endless possibilities to create stories that are rich. About SIMS 4The Sims 4 is a life simulation game developed by Maxis and published by Electronic Arts. Game key generator sims 4. Enjoy it play SIMS 4 online.Video instruction – watch the step by stepSTEP – 1.
Encryption Rsa 2048 Key Generated For This Computer Game
Different keys are used for encryption and decryption. This is a property which set this scheme different than symmetric encryption scheme.
Each receiver possesses a unique decryption key, generally referred to as his private key.
Receiver needs to publish an encryption key, referred to as his public key.
Some assurance of the authenticity of a public key is needed in this scheme to avoid spoofing by adversary as the receiver. Generally, this type of cryptosystem involves trusted third party which certifies that a particular public key belongs to a specific person or entity only.
Encryption algorithm is complex enough to prohibit attacker from deducing the plaintext from the ciphertext and the encryption (public) key.
Though private and public keys are related mathematically, it is not be feasible to calculate the private key from the public key. In fact, intelligent part of any public-key cryptosystem is in designing a relationship between two keys.
There are three types of Public Key Encryption schemes. We discuss them in following sections −
RSA Cryptosystem
This cryptosystem is one the initial system. It remains most employed cryptosystem even today. The system was invented by three scholars Ron Rivest, Adi Shamir, and Len Adleman and hence, it is termed as RSA cryptosystem.
We will see two aspects of the RSA cryptosystem, firstly generation of key pair and secondly encryption-decryption algorithms.
Generation of RSA Key Pair
Each person or a party who desires to participate in communication using encryption needs to generate a pair of keys, namely public key and private key. The process followed in the generation of keys is described below −
Generate the RSA modulus (n)
Select two large primes, p and q.
Calculate n=p*q. For strong unbreakable encryption, let n be a large number, typically a minimum of 512 bits.
Find Derived Number (e)
Number e must be greater than 1 and less than (p − 1)(q − 1).
There must be no common factor for e and (p − 1)(q − 1) except for 1. In other words two numbers e and (p – 1)(q – 1) are coprime.
Form the public key
The pair of numbers (n, e) form the RSA public key and is made public.
Interestingly, though n is part of the public key, difficulty in factorizing a large prime number ensures that attacker cannot find in finite time the two primes (p & q) used to obtain n. This is strength of RSA.
Generate the private key
Private Key d is calculated from p, q, and e. For given n and e, there is unique number d.
Number d is the inverse of e modulo (p - 1)(q – 1). This means that d is the number less than (p - 1)(q - 1) such that when multiplied by e, it is equal to 1 modulo (p - 1)(q - 1).
This relationship is written mathematically as follows −
The Extended Euclidean Algorithm takes p, q, and e as input and gives d as output.
Example
An example of generating RSA Key pair is given below. (For ease of understanding, the primes p & q taken here are small values. Practically, these values are very high).
Let two primes be p = 7 and q = 13. Thus, modulus n = pq = 7 x 13 = 91.
Select e = 5, which is a valid choice since there is no number that is common factor of 5 and (p − 1)(q − 1) = 6 × 12 = 72, except for 1.
The pair of numbers (n, e) = (91, 5) forms the public key and can be made available to anyone whom we wish to be able to send us encrypted messages.
Input p = 7, q = 13, and e = 5 to the Extended Euclidean Algorithm. The output will be d = 29.
Check that the d calculated is correct by computing −
Hence, public key is (91, 5) and private keys is (91, 29).
Encryption and Decryption
Once the key pair has been generated, the process of encryption and decryption are relatively straightforward and computationally easy.
Interestingly, RSA does not directly operate on strings of bits as in case of symmetric key encryption. It operates on numbers modulo n. Hence, it is necessary to represent the plaintext as a series of numbers less than n.
RSA Encryption
Suppose the sender wish to send some text message to someone whose public key is (n, e).
The sender then represents the plaintext as a series of numbers less than n.
To encrypt the first plaintext P, which is a number modulo n. The encryption process is simple mathematical step as −
In other words, the ciphertext C is equal to the plaintext P multiplied by itself e times and then reduced modulo n. This means that C is also a number less than n.
Returning to our Key Generation example with plaintext P = 10, we get ciphertext C −
RSA Decryption
The decryption process for RSA is also very straightforward. Suppose that the receiver of public-key pair (n, e) has received a ciphertext C.
Receiver raises C to the power of his private key d. The result modulo n will be the plaintext P.
Returning again to our numerical example, the ciphertext C = 82 would get decrypted to number 10 using private key 29 −
RSA Analysis
The security of RSA depends on the strengths of two separate functions. The RSA cryptosystem is most popular public-key cryptosystem strength of which is based on the practical difficulty of factoring the very large numbers.
Encryption Function − It is considered as a one-way function of converting plaintext into ciphertext and it can be reversed only with the knowledge of private key d.
Key Generation − The difficulty of determining a private key from an RSA public key is equivalent to factoring the modulus n. An attacker thus cannot use knowledge of an RSA public key to determine an RSA private key unless he can factor n. It is also a one way function, going from p & q values to modulus n is easy but reverse is not possible.
If either of these two functions are proved non one-way, then RSA will be broken. In fact, if a technique for factoring efficiently is developed then RSA will no longer be safe.
The strength of RSA encryption drastically goes down against attacks if the number p and q are not large primes and/ or chosen public key e is a small number.
ElGamal Cryptosystem
Along with RSA, there are other public-key cryptosystems proposed. Many of them are based on different versions of the Discrete Logarithm Problem.
ElGamal cryptosystem, called Elliptic Curve Variant, is based on the Discrete Logarithm Problem. It derives the strength from the assumption that the discrete logarithms cannot be found in practical time frame for a given number, while the inverse operation of the power can be computed efficiently.
Let us go through a simple version of ElGamal that works with numbers modulo p. In the case of elliptic curve variants, it is based on quite different number systems.
Generation of ElGamal Key Pair
Each user of ElGamal cryptosystem generates the key pair through as follows −
Choosing a large prime p. Generally a prime number of 1024 to 2048 bits length is chosen.
Choosing a generator element g.
This number must be between 1 and p − 1, but cannot be any number.
It is a generator of the multiplicative group of integers modulo p. This means for every integer m co-prime to p, there is an integer k such that gk=a mod n.
For example, 3 is generator of group 5 (Z5 = {1, 2, 3, 4}).
| N | 3n | 3n mod 5 |
|---|---|---|
| 1 | 3 | 3 |
| 2 | 9 | 4 |
| 3 | 27 | 2 |
| 4 | 81 | 1 |
Choosing the private key. The private key x is any number bigger than 1 and smaller than p−1.
Computing part of the public key. The value y is computed from the parameters p, g and the private key x as follows −
Obtaining Public key. The ElGamal public key consists of the three parameters (p, g, y).
For example, suppose that p = 17 and that g = 6 (It can be confirmed that 6 is a generator of group Z17). The private key x can be any number bigger than 1 and smaller than 71, so we choose x = 5. The value y is then computed as follows −
Thus the private key is 62 and the public key is (17, 6, 7).
Encryption and Decryption
The generation of an ElGamal key pair is comparatively simpler than the equivalent process for RSA. But the encryption and decryption are slightly more complex than RSA.
ElGamal Encryption
Suppose sender wishes to send a plaintext to someone whose ElGamal public key is (p, g, y), then −
Sender represents the plaintext as a series of numbers modulo p.
To encrypt the first plaintext P, which is represented as a number modulo p. The encryption process to obtain the ciphertext C is as follows −
- Randomly generate a number k;
- Compute two values C1 and C2, where −
Send the ciphertext C, consisting of the two separate values (C1, C2), sent together.
Referring to our ElGamal key generation example given above, the plaintext P = 13 is encrypted as follows −
- Randomly generate a number, say k = 10
- Compute the two values C1 and C2, where −
Send the ciphertext C = (C1, C2) = (15, 9).
ElGamal Decryption
To decrypt the ciphertext (C1, C2) using private key x, the following two steps are taken −
Compute the modular inverse of (C1)x modulo p, which is (C1)-x , generally referred to as decryption factor.
Obtain the plaintext by using the following formula −
In our example, to decrypt the ciphertext C = (C1, C2) = (15, 9) using private key x = 5, the decryption factor is
Extract plaintext P = (9 × 9) mod 17 = 13.
Encryption Rsa 2048 Key Generated For This Computer Windows 7
ElGamal Analysis
In ElGamal system, each user has a private key x. and has three components of public key − prime modulus p, generator g, and public Y = gx mod p. The strength of the ElGamal is based on the difficulty of discrete logarithm problem.
The secure key size is generally > 1024 bits. Today even 2048 bits long key are used. On the processing speed front, Elgamal is quite slow, it is used mainly for key authentication protocols. Due to higher processing efficiency, Elliptic Curve variants of ElGamal are becoming increasingly popular.
2048 Bit Rsa Key
Elliptic Curve Cryptography (ECC)
Elliptic Curve Cryptography (ECC) is a term used to describe a suite of cryptographic tools and protocols whose security is based on special versions of the discrete logarithm problem. It does not use numbers modulo p.
ECC is based on sets of numbers that are associated with mathematical objects called elliptic curves. There are rules for adding and computing multiples of these numbers, just as there are for numbers modulo p.
ECC includes a variants of many cryptographic schemes that were initially designed for modular numbers such as ElGamal encryption and Digital Signature Algorithm.
Rsa 2048 Bit Encryption
It is believed that the discrete logarithm problem is much harder when applied to points on an elliptic curve. This prompts switching from numbers modulo p to points on an elliptic curve. Also an equivalent security level can be obtained with shorter keys if we use elliptic curve-based variants.
The shorter keys result in two benefits −
- Ease of key management
- Efficient computation
These benefits make elliptic-curve-based variants of encryption scheme highly attractive for application where computing resources are constrained.
RSA and ElGamal Schemes – A Comparison
Let us briefly compare the RSA and ElGamal schemes on the various aspects.
| RSA | ElGamal |
|---|---|
| It is more efficient for encryption. | It is more efficient for decryption. |
| It is less efficient for decryption. | It is more efficient for decryption. |
| For a particular security level, lengthy keys are required in RSA. | For the same level of security, very short keys are required. |
| It is widely accepted and used. | It is new and not very popular in market. |