Generating Your SSH Public Key. In order to provide a public key, each user in your system must generate one if they don’t already have one. See the GitHub.
- Generate A Ssh Key On Mac For Github Account
- Mac Os Generate Ssh Key
- Generate A Ssh Key On Mac For Github Mac
- Generate A Ssh Key On Mac For Github Free
- Github Get Ssh Key
Create an SSH key pair. Use the ssh-keygen command to generate SSH public and private key files. By default, these files are created in the /.ssh directory. You can specify a different location, and an optional password (passphrase) to access the private key file. If an SSH key pair with the same name exists in the given location, those files are overwritten. If you don't have an existing public and private key pair, or don't wish to use any that are available to connect to GitHub, then generate a new SSH key. If you see an existing public and private key pair listed (for example idrsa.pub and idrsa) that you would like to use to connect to GitHub, you can add your SSH key to the ssh-agent.
This is a brief guide to creating a public/private key pair that can be used for OpenSSL.While the 'easy' version will work, I find it convenient to generate a single PEM bundleand then export the private/public key from that as needed. This document also covers howto add and remove a password from your private key and how to make sure that keychainwill automatically unlock it when you sign in.
Just make it work
Generate an ssh key-pair:
If you just pound enter through the setup procedure then you will end up with a new keypair created in the default location: /Users/yourname/.ssh/. There will be two files:
id_rsaThis is your private key, you must keep it secret and never allow anybodyelse to gain control of it. Treat this key like a password, keep it safe and makea backup copy. You can add it to keychain usingssh-add -K ~/.ssh/id_rsa.id_rsa.pubThis is your public key, you can share it freely. This part of the keyis used during authentication to encode a message which can only be decoded with theprivate key. It cannot be used to derive the private key so there is no risk insharing it.
When a server administrator asks for a copy of your public key, send them a copy of theid_rsa.pub file. They'll be able to add it to your user account's list of authorizedkeys and that will enable you to log in without typing a password.
Doing it the hard way
This method involves creating the keys as a bundle, exporting the public key andmanually setting the permssions on all of the paths. You'll also have to configureOpenSSH to use your new bundle for authentication.
A summary of the steps follows:
Rational
I prefer to generate a certificate using OpenSSL directly, then export the private orpublic-key in the necessary format as needed. The benefits to this appraoch are three-fold:
- This is a process similar to the one you'd use to generate certificates used forother tasks like S/MIME or to become part of a signed certificate for HTTPS.
- There is a single certificate file from which you can derive the private or publickey in whichever format you need. It's much easier to manage one key than two, oreven several if you require the key in different formats.
- You gain control over the key length, encryption method, and algorithm so that youcan consciously decide to use weaker keys for old/slow hardware (e.g. the RaspberryPi media server in your closet) and strong but slower keys where appropriate.
Default software and Mac OS X
In order to generate the key I prefer to use OpenSSL directly rather than the ssh-keygen tool.While it is possible to provide flags to ssh-keygen using OpenSSL gives us access to optionsthat are not avaiable in the standard Mac OS X version of SSH but doesn't require us to buildthe SSH client from scratch.
Update OpenSSL
Unfortunately the version of OpenSSL that ships with Mac OS x is rather dated and so it'smissing some of the features of the latest versions. One of those features is the genpkeycommand which is the new recommended way to generate keys. Assuming you have Homebrewinstalled (see: https://brew.sh) you can install an up-to-date version of OpenSSL with:
Many packages that you install with homebrew are likely to depend on OpenSSL anyway so thisis not a terrible idea even if you don't care about using OpenSSL directly.
Updating OpenSSH
If you're interested in rebuilding openssh you should link against LibreSSL sothat passwords can be installed in your keychain.
This is a relatively new option and caution should be taken because compatibilitymay not be perfect. LibreSSL is not intended to be a 1:1 replacement for OpenSSL.
It appears that just building OpenSSH will not have it request key information fromthe Mac OS X keychain, nor will it automatically start SSH-Agent so there may besome trouble-shooting steps required if you prefer to go this path. I do not builda new version of SSH.
Creating directories
OpenSSH requires that keys be stored in ~/.ssh and that path must be restrictedso that only the user can access it. It also requires that any identify files beaccessible only by the user too. Permssions for ~/.ssh/config can be more relaxedbut it is good practice to keep those private so as not to leak inforamtion aboutuser names or servers you connect to.
Create the directories by running:
While this will create the directory you will have to modify the default permissions.Read/write/execute for the owner and no access for any other user is required. Recall,the execute flag on a directory allows you to view its content.
You might want to create an empty ssh config file and set appropriatepermissions so that you don't have to remember how to do it later whenthere's some problem and you are half-asleep, drunk, and responding to aPagerDuty alert.
You can save a few copy steps if you're following this guide by changinginto your ssh path for the remaining steps:
Generating keys
The first step to generating keys is to create the bundle using OpenSSL. Thisapproach allows us to specify a few extra options when creating keys that arenormally hidden by ssh-keygen:
The options: are
genpkeyis the new command for generating keys, it supercedes the oldgenrsamethod. Mac OS X's default OpenSSL does not have this command sobuilding your own version is required.-algorith rsauses the RSA algorithm for the key and is recommended formaximum compatibility. Other options includeECDSA, which is lesscomputationally intensive on very low-end hardware (e.g. 50 MHz ARM) andDHwhich has characteristics similar to RSA but is rarely used.-aes-256-cbcis the cypher used to encrypt the bundle and causes the userto be prompted for a password. There are a number of available ciphers butAES-256-cbc is among the stronger options available and widely used too.-outform PEMthere are several output formats that you can use but PEM iswidely used by open source software and tends to be the best supported. Theformat is also nicely encoded so that you can debug with any text editor andhas the advantage of bundling the public and private key into a single filewhich makes them easier to move around. You can always output the public orprivate key from a PEM bundle that contains both.-pkey_opt …can be specified multiple times and supplies options to thegeneration function. This can be specified multiple times to suplly severaloptionsrsa_keygen_bits:4096sets the length of the keys produced. 1024 bits isgenerally considered the absolute minimum for secure communication todaythough there is some concern that they will be broken for well-fundedattackers in the near future so 2048 bits is recommended where possible.Longer keys provide greater security however there is diminishing returnsas key length increases. Also, increasing the key length also increasescomputational costs exponentially (by the cube of the change, so 2048 is8x more demanding than 1024-bit). You may want to use smaller keys forslower hardware or if you find yourself frequently reconnecting due to badconnections during a session for better performance.
-out yourname.pemdefines the output file for your bundle. You should storea copy of this certificate in~/.sshso that it can be used to authenticatessh sessions. The file must not be accessible to other users on the system soset the permissions accordingly. You should also store the file and thepassword somewhere safe (like in your password vault or on a USB drive in asafe deposit box).
When generating the key you will be prompted for a password. Make sure to use a verystrong, unique, random password for this file. You won't have to type it in regularlyso generate it with your password vault. In a pinch you can generate a random passwordusing OpenSSL via: openssl rand -base64 48.
When the bundle has been generated, copy it to your~/.ssh folder and change itspermissions accordingly:
I prefer to make the bundle read-only for my user so I never accidentally edit it orstrip the password. chmod 0600 ~/.ssh/yourname.pem would also work if you don't mindit being editable by your user.
Extracting the public key
You'll want to be able to send the public key to other people and leave it on othercomputers without risking your private key. The easiest way to export your publickey is using the ssh-keygen method which prints it to standard out.
You can always redirect that to a file if you want to send it via email or copy itvia SFTP. Generally I prefer not to keep a copy of my public keys on disk so that I amjustified in always treating ~/.ssh as a secret.
Configuring OpenSSH
Remember to either edit your ~/.ssh/config to specify this bundle as the defaultidentify file by adding the line:
Alternatively you can specify it on a host-by-host basis by using ssh command-lineoptions: ssh -i ~/.ssh/yourname.pem example.com -l someuser. When you areprompted for a password, remember that you should enter the one used when creatingthe bundle, not the log-in password for your computer or the remote system you areconnecting to.
Finally, you should consider adding the key to your Mac OX X keychain using:
This will store the password in the login Keychain which is unlocked automaticallywhenever you sign in. Storing your password this way means you won't have to re-typethe password you used when creating the bundle in order to use it.
Generate A Ssh Key On Mac For Github Account
Using ssh -i ~/.ssh/yourname.pem foo.example.com will also add your key to Keychain.
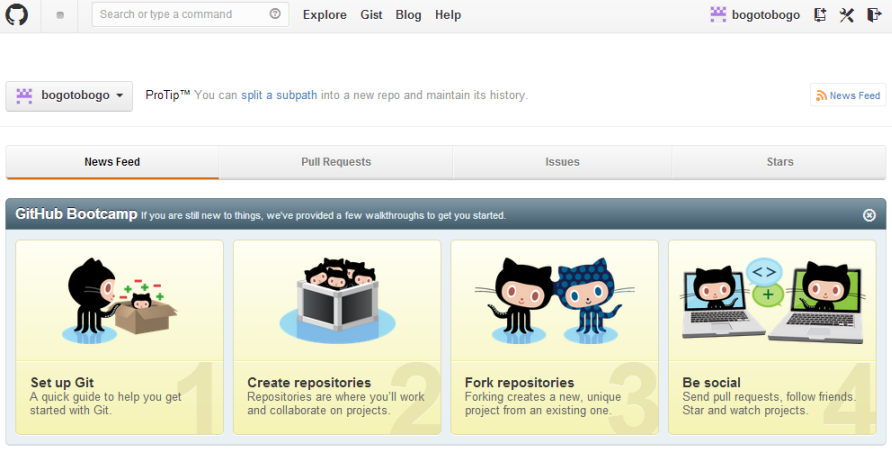
Public Keys and Github.com
It's a good idea to add your public key to github.com so that you can pull from privaterepositories and push changes to your public repositories. You can do this at:
Once you've uploaded your public key, other users can download it by going to
For example, my public key is located here: https://github.com/colinstein.keys
Mac Os Generate Ssh Key
You may want to create different key-pairs for different repositories or organizationsand then use ~/.ssh/config and local .gitconfig files ot manage those relationships.
After generating keys in the above manner for each github account you can configuressh by editing ~/.ssh/config and adding entries like the following for each account:
When cloing a repository you would then clone from the appropriate host:
You can also edit the existing git remote by editing the .gitconfig insidethe checked out repository:
Git also provides a number of ways to configure SSH via git config andgit remote add foo git@github.com-foo:somegithubuser/somerepo.git. A fullrun through of those options is well outside the scope of this gist.
You generate an SSH key through Mac OS X by using the Terminal application. Once you upload a valid public SSH key,Gerrit can authenticate you based on this key.
The SIMS 3 Free CD Key Generator. This The SIMS 3 Code Giveaway Tool is refreshed, tried, and working. Not any more fake records that will squander your valuable time and cash. The SIMS 3 online code generator works flawlessly and has been tried on. May 27, 2017 The Sims 3 Serial Key Download Code Crack key generator Full Game Torrent skidrow Origin Key and Steam Online Code Avaiable. The Sims 3 Serial Key Cd Key Free Download Crack Full Game The Sims 3 Serial Cd Key Generator License Activator Product Origin Keys. The sims 3 product key generator. The Sims 3 Seasons Keygen Activation Key Generator With no further hold up, we acquaint with you The Sims 3 Seasons CD Key Generator, have the capacity to play The Sims 3 Seasons free! This program will have the capacity to produce the same number of CD key codes for The Sims 3 Seasons and to play it without breaks and different staffs.
An SSH key consists of a pair of files. One is the private key, which you should never give to anyone. No one will everask you for it and if so, simply ignore them - they are trying to steal it.The other is the public key. When you generate your keys, you will use ssh-keygen to store the keys in a safe locationso you can authenticate with Gerrit.
To generate SSH keys in Mac OS X, follow these steps:
Enter the following command in the Terminal window:
This starts the key generation process. When you execute this command, the ssh-keygen utility prompts you to indicate where to store the key.
Press the
ENTERkey to accept the default location. The ssh-keygen utility prompts you for a passphrase.Type in a passphrase. You can also hit the
ENTERkey to accept the default (no passphrase). However, this is not recommended.
Warning
You will need to enter the passphrase a second time to continue.
Generate A Ssh Key On Mac For Github Mac
After you confirm the passphrase, the system generates the key pair and you will see output like this:
Your private key is saved to the id_rsa file in the .ssh subdirectory of your home directory and is used to verifythe public key you use belongs to your Gerrit account.
Warning
Never share your private key with anyone! Ever! We mean it!
Your public key is saved to a file called id_rsa.pub in the .ssh subdirectory of your home directory. You can copyit to your clipboard using the following command:
Now you can head over to Gerrit, go to settings and paste your public key as described here.
Generate A Ssh Key On Mac For Github Free
Gerrit is using the special port 29418 instead of the default SSH port 22 which has to be configured accordingly. This can be done in your local ~/.ssh/config file which would contain the following sections then:
Github Get Ssh Key
Testing your connection: