- Cryptography Tutorial
- Lack Of Randomness In The Key Generation Process Of Life
- Lack Of Randomness In The Key Generation Process 2
- Lack Of Randomness In The Key Generation Processor
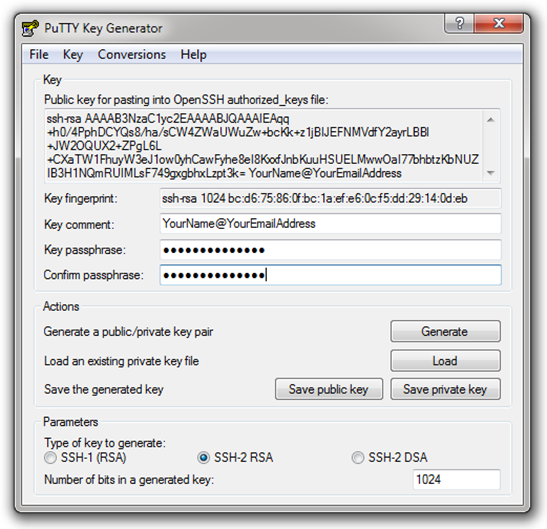
Easy-to-guess values) as the seed for its pseudo-random num-ber generator. This bug caused affected machines to select a 1024-bit RSA modulus from a pool of fewer than one million values, rather than the near-21000 possible values 45. By replaying the key generation process using each of the one. When used with asymmetric ciphers for key transfer, pseudorandom key generators are nearly always used to generate the symmetric cipher session keys. However, lack of randomness in those generators or in their initialization vectors is disastrous and has led to cryptanalytic breaks in the past. Distributed key generation: For some protocols, no party should be in the sole possession of the secret key. Rather, during distributed key generation, every party obtains a share of the key. A threshold of the participating parties need to cooperate to achieve a cryptographic task, such as decrypting a message.
At the heart of all cryptographic systems is the generation of secret, unguessable (i.e., random) numbers. The lack of generally available facilities for generating such random numbers (that is, the lack of general availability of truly unpredictable sources) forms an open wound in the design of cryptographic software. Modality to generate random sequences using software method. Unpredictable random number generator mimic a practical approximation of true random number generator. It extracts randomness from easily available devices. It based on the behavior of hardware devices. The intervention in the generation process disturbs the internal state.
- Cryptography Useful Resources
- Selected Reading
The Data Encryption Standard (DES) is a symmetric-key block cipher published by the National Institute of Standards and Technology (NIST).
DES is an implementation of a Feistel Cipher. It uses 16 round Feistel structure. The block size is 64-bit. Though, key length is 64-bit, DES has an effective key length of 56 bits, since 8 of the 64 bits of the key are not used by the encryption algorithm (function as check bits only). General Structure of DES is depicted in the following illustration −
Since DES is based on the Feistel Cipher, all that is required to specify DES is −
Lack Of Randomness In The Key Generation Process Of Life
- Round function
- Key schedule
- Any additional processing − Initial and final permutation
Initial and Final Permutation
The initial and final permutations are straight Permutation boxes (P-boxes) that are inverses of each other. They have no cryptography significance in DES. The initial and final permutations are shown as follows −
Round Function
The heart of this cipher is the DES function, f. The DES function applies a 48-bit key to the rightmost 32 bits to produce a 32-bit output.
Expansion Permutation Box − Since right input is 32-bit and round key is a 48-bit, we first need to expand right input to 48 bits. Permutation logic is graphically depicted in the following illustration −
The graphically depicted permutation logic is generally described as table in DES specification illustrated as shown −
XOR (Whitener). − After the expansion permutation, DES does XOR operation on the expanded right section and the round key. The round key is used only in this operation.
Substitution Boxes. − The S-boxes carry out the real mixing (confusion). DES uses 8 S-boxes, each with a 6-bit input and a 4-bit output. Refer the following illustration −
The S-box rule is illustrated below −
Franklin can drive a car in a “gradual-mo.” And Trevor, fighting with combatants in the close fight, without difficulty switches to berserker mode. Each of these competencies is tied to a different counter, as it fills up, it turns into more potent. Each of the main characters has a unique skill that may be used in an essential state of affairs. The key distinction between GTA 5 key code and other video games inside the series is the three protagonists. GTA 5 Crack Free DownloadGTA 5 key code is an action-packed game approximately the thrilling adventures of 3 buddies-robbers inside the massive metropolis of Los Santos (primarily based on real Los Angeles) and its surroundings, such as the entire district of Blaine with beautiful forests, lakes, deserts, and various attractions. Gta v free no survey key generator.
There are a total of eight S-box tables. Adobe photoshop cs 8.0 torrent. The output of all eight s-boxes is then combined in to 32 bit section.
Straight Permutation − The 32 bit output of S-boxes is then subjected to the straight permutation with rule shown in the following illustration:
Key Generation
The round-key generator creates sixteen 48-bit keys out of a 56-bit cipher key. The process of key generation is depicted in the following illustration −
The logic for Parity drop, shifting, and Compression P-box is given in the DES description.
DES Analysis
The DES satisfies both the desired properties of block cipher. These two properties make cipher very strong.
Lack Of Randomness In The Key Generation Process 2
Avalanche effect − A small change in plaintext results in the very great change in the ciphertext.
Completeness − Each bit of ciphertext depends on many bits of plaintext.
During the last few years, cryptanalysis have found some weaknesses in DES when key selected are weak keys. These keys shall be avoided.
Lack Of Randomness In The Key Generation Processor
DES has proved to be a very well designed block cipher. There have been no significant cryptanalytic attacks on DES other than exhaustive key search.